So, wanted to be able to set an expiry longer than 7 days (max for a signed url from s3)
First, make yourself an S3 bucket 🙂
Following this tutorial https://dev.to/idrisrampurawala/share-your-aws-s3-private-content-with-others-without-making-it-public-4k59
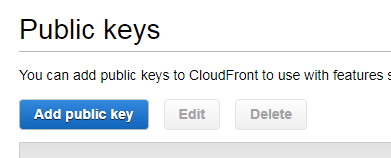
First needed to create a public key.
Easiest way on windows if you have git installed is to use the handy dandy version of openssl here
C:\Program Files\Git\usr\bin\
Create and upload the public key
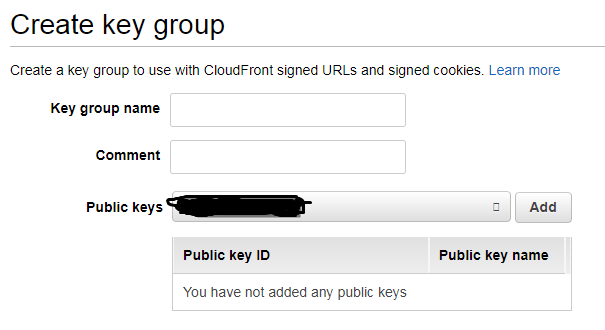
Create the Trusted Key Group and add the key you made
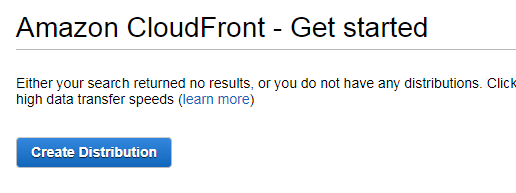
Now create a cloud front distribution. They have a handy drop down to select your bucket and it fills in Origin ID
Choose Restrict Bucket Access (That’s the whole point!)
Create a new identity, and have it update the bucket policy.
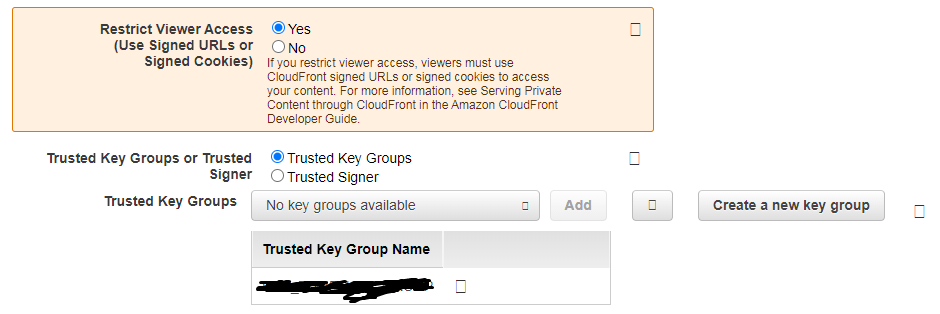
Restrict Viewer Access
(Use Signed URLs or
Signed Cookies)
Set to True
Choose to Used Trusted Key Groups, and add the key made above.
—
Put the private key into secrets manager
Wait until the distribution shows enabled, now create your lambda.
So I actually like this code sample the best https://docs.aws.amazon.com/AmazonCloudFront/latest/DeveloperGuide/PrivateCFSignatureCodeAndExamples.html
And
https://github.com/boto/boto3/blob/develop/boto3/examples/cloudfront.rst
You of course need a copy of cryptography
Here is one if you trust a random stranger (Shout out to Javier!) -> https://github.com/mellerbeck/cryptography
There were two things that tripped me up. The first,
# cloudfront key-par access ID generated in step 1
key_id = <your-cloudfront-key-par-access-ID>
This is the ID of the public key you uploaded (NOT the distribution ID)
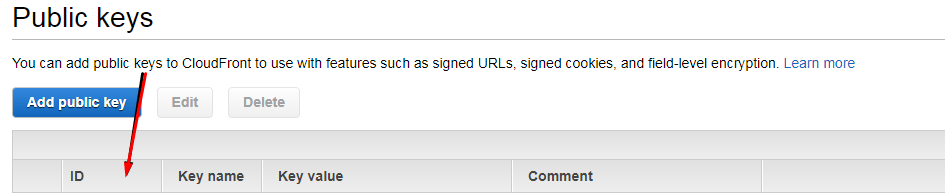
This column from the Public Keys screen
The second,
# your cloudfront distribution domain created in step 4 of distribution creation steps
cloudfront_domain = <your-cloudfront-distribution-domain>
You need to include https:// in this variable, or you get accessed denied!
This was my clue https://github.com/boto/boto3/blob/develop/boto3/examples/cloudfront.rst
Also, looks like for cloudfront the expiration is set to a linux epoch time in seconds.
Good luck!